WordPress is powerful and secure at its core. Any potential vulnerabilities are patched by its security team fast.
But when you consider all the extensions and themes that enhance its functionality, it is no longer as secure.
So you need to do your part to secure your site.
While tips like “use a strong password” are common, this guide will help you establish a deeper layer of security with lesser known strategies for WordPress security.
Here is the definitive WordPress security checklist for high-level security on your website:
1. Protect important Files using .htaccess.
.htaccess is an important file that configures your server and controls the security of your entire website. It also controls the use of permalinks on your website.
Using .htaccess you can restrict access to important files. Here are the steps:
- .htaccess file is hidden by default in the server’s root directory. To access it, change your FTP client settings to display hidden files. If you use FileZilla, go to Server > Force showing hidden files.
- Once you have located the file, insert the following code outside the #BEGIN WordPress and #END WordPress tags.
<FilesMatch "^.*(error_log|wp-config\.php|php.ini|\.[hH][tT][aApP].*)$"> Order deny,allow Deny from all </FilesMatch>
This code restricts access to sensitive files such as wp-config.php, php.ini, error logs and .htaccess itself.
Note: Modify the php.ini file name if needed. (e.g. php5.ini or php7.ini).
2. Keep track of Dashboard activity
If you have multiple users on your website, it is important to know what they are up to.
Even if the users aren’t involved in any suspicious actions, tracking their activity can help you avoid accidental errors and shutdowns. And if a hacker is trying to break in, you will be prepared for it.
WordPress creates automatic logs of such activity.

But you are better off using a plugin to have the data organized. A good plugin to check out is WP Security Audit Log.
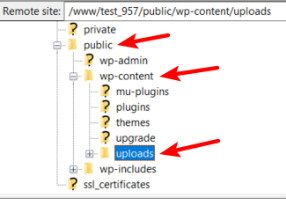
3. Prevent PHP Execution in the Uploads folder.
Hackers often intrude into a site by uploading scripts in certain parts of your WordPress directories. One of them is the uploads folder.
The uploads folder contains the files you upload through the media center or WordPress security plugins. For example, when the the MailPoet plugin was hacked, it gave hackers the power to execute malware into the uploads folder even without admin permissions.
To secure this folder, you need to
- Create a new .htaccess file in the wp-content/uploads directory.
- Add the following code to the .htaccess file:
# Kill PHP Execution <Files ~ "\.ph(?:p[345]?|t|tml)$"> deny from all </Files>
4. Limit User Access
To give users access to your website, follow ‘the principle of least privilege’.
It means giving only as much control as needed to do the job. For example, a writer shouldn’t be able to install new WordPress security plugins. A chat agent shouldn’t be able to edit pages.
You need to distribute user roles well so that high-level control of your website is in the hands of people you trust.

5. Disable XML-RPC
XML-RPC is a feature that allows you to access WordPress remotely. You can also use it for trackbacks and pingbacks.
Since it allows connectivity, hackers can use it to run brute force attacks, launch a DDoS attack or spam your site with trackbacks and pingbacks.
If you aren’t going to use its features, it is better to disable XML-RPC. To do so, you can use the Disable XML-RPC plugin.
If you need the features of XML-RPC, you can still make it secure by removing some XML-RPC methods that are used by hackers. This can be done easily by installing the Disable XML-RPC Pingback Plugin
6. Check for known vulnerabilities
You should be aware of the vulnerabilities that come up in WordPress. The more you know about potential attacks and vulnerabilities, the better you can secure your site.
Keep yourself updated on potential vulnerabilities using this free database: WPScan Vulnerability Database
7. Hide your WordPress Version
WordPress has a meta tag in its source code that displays the version of your site.
If hackers get hold of this information, they can use it to expose vulnerability and plan an attack against your site.
So it is essential to hide the version number. To do so, you can simply add the following code to the function.php file:
function remove_wordpress_version_number() {
return '';
}
add_filter('the_generator', 'remove_wordpress_version_number');
function remove_version_from_scripts( $src ) {
if ( strpos( $src, 'ver=' . get_bloginfo( 'version' ) ) )
$src = remove_query_arg( 'ver', $src );
return $src;
}
add_filter( 'style_loader_src', 'remove_version_from_scripts');
add_filter( 'script_loader_src', 'remove_version_from_scripts');
8. Limit access to login page using .htaccess file
If you want to implement rigorous security measures on your site, one of the most effective ways is to block access to wp-admin and wp-login.php pages.
You can still keep access open for the IP addresses you use. Just add the following code to your .htaccess file:
<IfModule mod_rewrite.c>
RewriteEngine on
RewriteCond %{REQUEST_URI} ^(.*)?wp-login\.php(.*)$ [OR]
RewriteCond %{REQUEST_URI} ^(.*)?wp-admin$
RewriteCond %{REMOTE_ADDR} !^Your IP address 1$
RewriteCond %{REMOTE_ADDR} !^ Your IP address 2$
RewriteCond %{REMOTE_ADDR} !^ Your IP address 3$
RewriteCond %{REMOTE_ADDR} !^ Your IP address 4$
RewriteCond %{REMOTE_ADDR} !^ Your IP address 5$
RewriteRule ^(.*)$ - [R=403,L]
</IfModule>
9. Disable Plugin and Theme Editor
The theme and plugin editor gives an easy way of editing themes and plugins right from the dashboard. But it is also prone to attack from hackers.
A small error in this editor can crash your website and block you from accessing your own site. Hackers can put in malicious code using the theme editor or gain access to a user account that has enough privileges to use the editor.
The solution is to disable the editor so that it can only be used with FTP access.
To implement this, simply add this code to the wp-config.php file:
define( 'DISALLOW_FILE_EDIT', true );
10. Auto-update Themes and Plugins
If you don’t update your theme and plugins, your site may develop vulnerabilities and hackers may take advantage of it.
If you do the updates on all themes and plugins manually, it will be time-consuming and boring. Plus if you forget to install an update, it may leave your website at risk.
You can set auto-updates by adding this code into the wp-config.php file.
For plugins, insert this code:
add_filter( 'auto_update_plugin', '__return_true' );
For themes, insert this code:
add_filter( 'auto_update_theme', '__return_true' );
11. Pick a Reliable Hosting Provider
You can install the smartest code for website security but if you don’t have a good hosting provider, your site will remain vulnerable to attacks.
So learn about different hosting providers and pick the best one.
It is better to choose dedicated WordPress hosting as it comes with WordPress firewall, updated PHP and mySQL, routine malware scans and support staff that knows WordPress in and out.
If you don’t have time for research, BlueHost is one of the most trusted names when it comes to site security.
12. Change the login error messages
If a hacker tries to log into your site, WordPress will tell them whether the username or the password is incorrect.

This information may look small, but it gives the hacker half of what they need to attack your site.
You can fix this by adding this code to your functions.php file.
function custom_wordpress_error_message(){
return 'That was not quite correct...';
}
add_filter( 'login_errors', 'custom_wordpress_error_message' );
13. Add Security Keys
WordPress uses security keys or SALTS to encrypt the data stored in browser cookies. This helps secure your password and other important information.
The keys are saved in the wp-config.php file and look like this:
define('AUTH_KEY', 'put your unique phrase here');
define('SECURE_AUTH_KEY', 'put your unique phrase here');
define('LOGGED_IN_KEY', 'put your unique phrase here');
You don’t have to come up with a unique key yourself. Just use the WordPress key generator.
14. Disable Script Injections
One way hackers launch an attack on your site is by inserting code into your php files. To guard against this, simply add this code to your existing php files:
Options +FollowSymLinks
RewriteEngine On
RewriteCond %{QUERY_STRING} (<|%3C).*script.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} GLOBALS(=|[|%[0-9A-Z]{0,2}) [OR]
RewriteCond %{QUERY_STRING} _REQUEST(=|[|%[0-9A-Z]{0,2})
RewriteRule ^(.*)$ index.php [F,L]
15. Secure wp-includes
Wp-includes has the crucial files needed to run the WordPress front end. It contains core files that should be way out of reach of any malicious elements.
To block access to wp-includes, add this code to your .htaccess file:
<IfModule mod_rewrite.c> RewriteEngine On RewriteBase / RewriteRule ^wp-admin/includes/ - [F,L] RewriteRule !^wp-includes/ - [S=3] RewriteRule ^wp-includes/[^/]+\.php$ - [F,L] RewriteRule ^wp-includes/js/tinymce/langs/.+\.php - [F,L] RewriteRule ^wp-includes/theme-compat/ - [F,L] </IfModule>
16. Hide author usernames
It is not that hard to dig up usernames on WordPress.
With little research, one can find the main author of a website.
Since the main author is usually the administrator, hackers may take advantage of this loophole to get administrative privileges.
To hide author usernames, add this code to the functions.php file:
add_action(‘template_redirect’, ‘bwp_template_redirect’);
function bwp_template_redirect()
{
if (is_author())
{
wp_redirect( home_url() ); exit;
}
}
17. Disable File Editing
If a hacker gets admin privileges somehow, they may edit the theme or plugin code of your website.
If you don’t use the file editing feature, it is better to disable it altogether.
To disable it, add this code to your wp-config.php file.
## Disable Editing in Dashboard 1. define(‘DISALLOW_FILE_EDIT’, true);
Conclusion:
Now that you have this wordpress security checklist, you don’t have to worry about your site getting compromised.




